Microsoft Entra ID SSO for Bookstack
ThisPrerequisites: guide shows how to integrate BookStack with Microsoft Entra ID.
Note If BookStack is used as a larger enterprise documentation platform, evaluate whether genericOIDCorSAMLis the better long-term choice. The built-in AzureAD social login is simple, but not always the most flexible option.
When this approach fits
Use this guide if:
Prerequisites
.envBookstack offers an OpenID interface, which means that Microsoft Entra ID can easily be used as an identity provider for managing access and permission within Bookstack. The functionalities are more limited than other integrations. However, simple functionalities such as automatic user creation and email verification can be customized.
This guide is a compilation of the main documentation of Bookstack: Third Party Authentication · BookStack (bookstackapp.com)
Create App Registration
First, an app registration including client secret must be created in Microsoft Entra ID
Stepsettings 1:can Createbe left at the appdefault registration
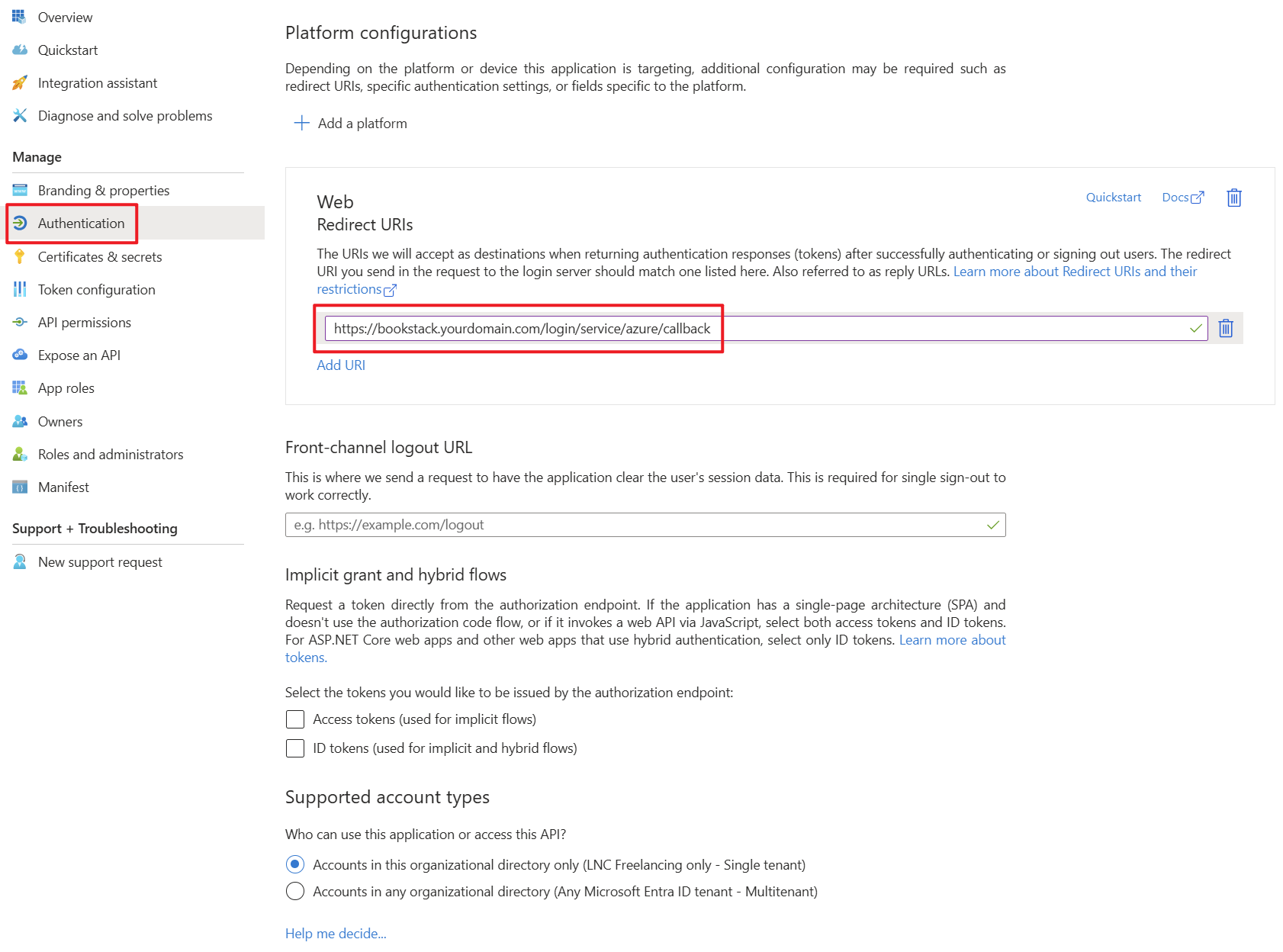
values. RecommendedImportant settings:settings are the Redirect URIs under the Authentication tab. Set these URIs to your external or internal domain on which Bookstack is available. These URIs will be used for Microsoft Entra ID to know where to redirect the user in case of successful logins.
Platform:Authentication Type:- Redirect
URI:URIs:https://<bookstack-domain>/bookstack.yourdomain.com/login/service/azure/callback
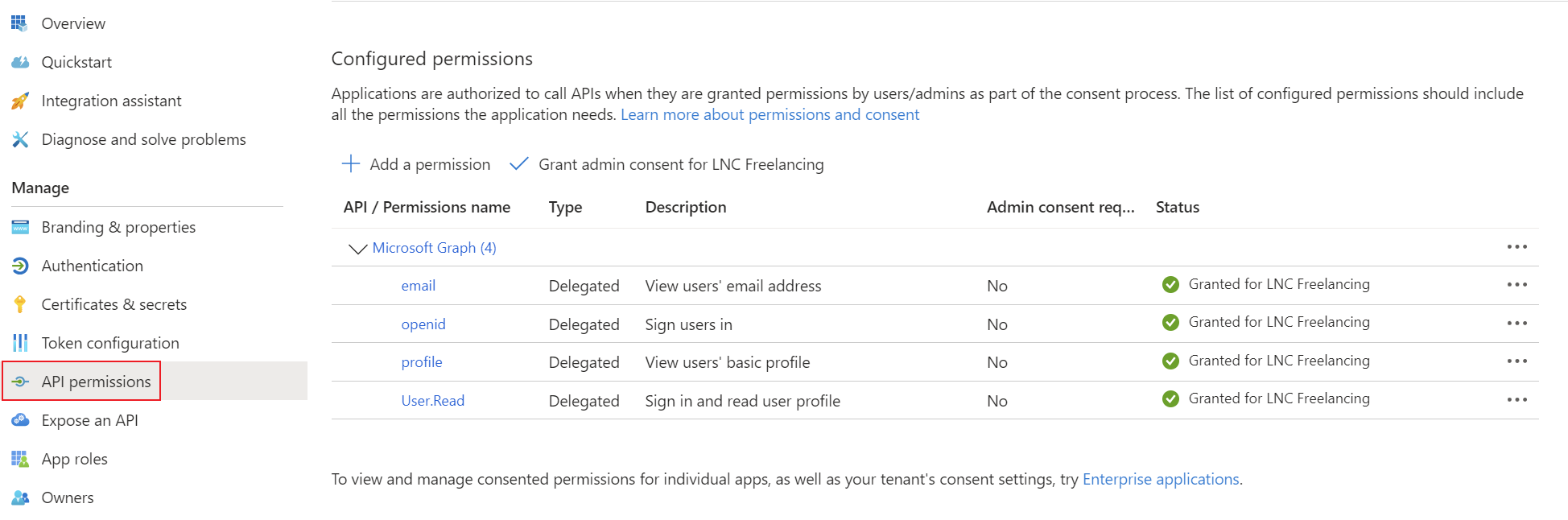
Add the Applicationcorresponding permissions for OpenID Connect as delegated permissions and grant admin consent for your tenant.
Create a client secret for the application and save the tenant ID, application ID and client secret in your password manager. You can find instructions for this information here: Get app details and grant permissions to app registration
Setup Microsoft Entra ID login provider
With Bookstack, the Microsoft Entra ID configurations can be set up using environment variables. Installation using Docker is mandatory for these instructions. The following environment variables enable the configuration of the OpenID integration.
The relevant environment variables for OpenID are as follows:
Stepfrom 2:the APIApp permissions
Registration.
ForSide note: As this logintype model,of User.Read
Docker compose example
This Docker Compose file shows a possible configuration for Bookstack that authenticates using Microsoft Entra ID. In addition, the database container and mail settings are also specified.
Customize this content with your specifications and save the content in a normal docker-compose.yaml file. As this is typicallyDocker sufficient.
Stepthe 3:application Configurecan BookStack
be Addstarted theseeasily variableswith tothe yourfollowing BookStackcommand .envordetach containermode configuration:-> -d):
docker compose up -dversion: "3"
services:
<yourbookstackcontainername>:
image: lscr.io/linuxserver/bookstack
container_name: <yourbookstackcontainername>
environment:
- PUID=1000
- PGID=1000
- APP_URL=https://<yourbookstackdomain>
- DB_HOST=<yourmariadbcontainername>
- DB_USER=<yourdbuser>
- DB_PASS=<yourdbpassword>
- DB_DATABASE=<yourdbname>
- MAIL_HOST=<yourmailserver>
- MAIL_PORT=587
- MAIL_FROM_NAME=<yourmailname>
- MAIL_FROM=<yoursmtpmail>
- MAIL_USERNAME=<yoursmtpmailuser>
- MAIL_PASSWORD=<yoursmtpmailpassword>
- AZURE_APP_ID=<client-idyourclientid>
- AZURE_APP_SECRET=<client-secretyourclientsecret>
- AZURE_TENANT=<tenant-idyourtenantid>
- AZURE_AUTO_REGISTER=true
- AZURE_AUTO_CONFIRM_EMAIL=true
volumes:
- <yourpersistentpathforbookstack>:/config
ports:
- 6875:80
restart: unless-stopped
depends_on:
- <yourmariadbcontainername>
<yourmariadbcontainername>:
image: lscr.io/linuxserver/mariadb
container_name: <yourmariadbcontainername>
environment:
- PUID=1000
- PGID=1000
- MYSQL_ROOT_PASSWORD=<yourdbrootpassword>
- TZ=<yourtimezone>
- MYSQL_DATABASE=<yourdbname>
- MYSQL_USER=<yourdbuser>
- MYSQL_PASSWORD=<yourdbpassword>
volumes:
- <yourpersistentpathformariadb>:/config
restart: unless-stoppedBest practices
Summary
The built-in Azure/Microsoft login in BookStack is a clean solution for simple internal SSO. For more advanced enterprise access models, evaluate OIDC or SAML.